Viewing network traffic calls on IOS real device using MITM Proxy
Getting Started
If you have used android studio for helping in setup emulators, you would have realized how nifty
the Logcat feature is. It allows us to see all network calls being made as we perform any user
journey on the mobile device. Ever wondered how to do this on an IOS real device? Xcode? Sadly we
do not have such a feature in Xcode. So what is the solution. Enter
MITM Proxy. For the uninitiated MITM is a
powerful HTTPS proxy which can be used for multiple use cases. Today lets see how we can use it to
capture traffic on an IOS real device.
Lets setup MITM
Installing and starting MITM proxy on mac
- Install MITM using homebrew
brew install mitmproxy - Run mitm proxy by typing
mitmproxyin terminal - Type
ifconfigand make a note of the machines IP address, printed inen0section. Alternatively you can also get the IP address by navigating toSystem Preferences > Network > Wifi > Advanced > IPV4
Setting up IOS real device to pass traffic via proxy
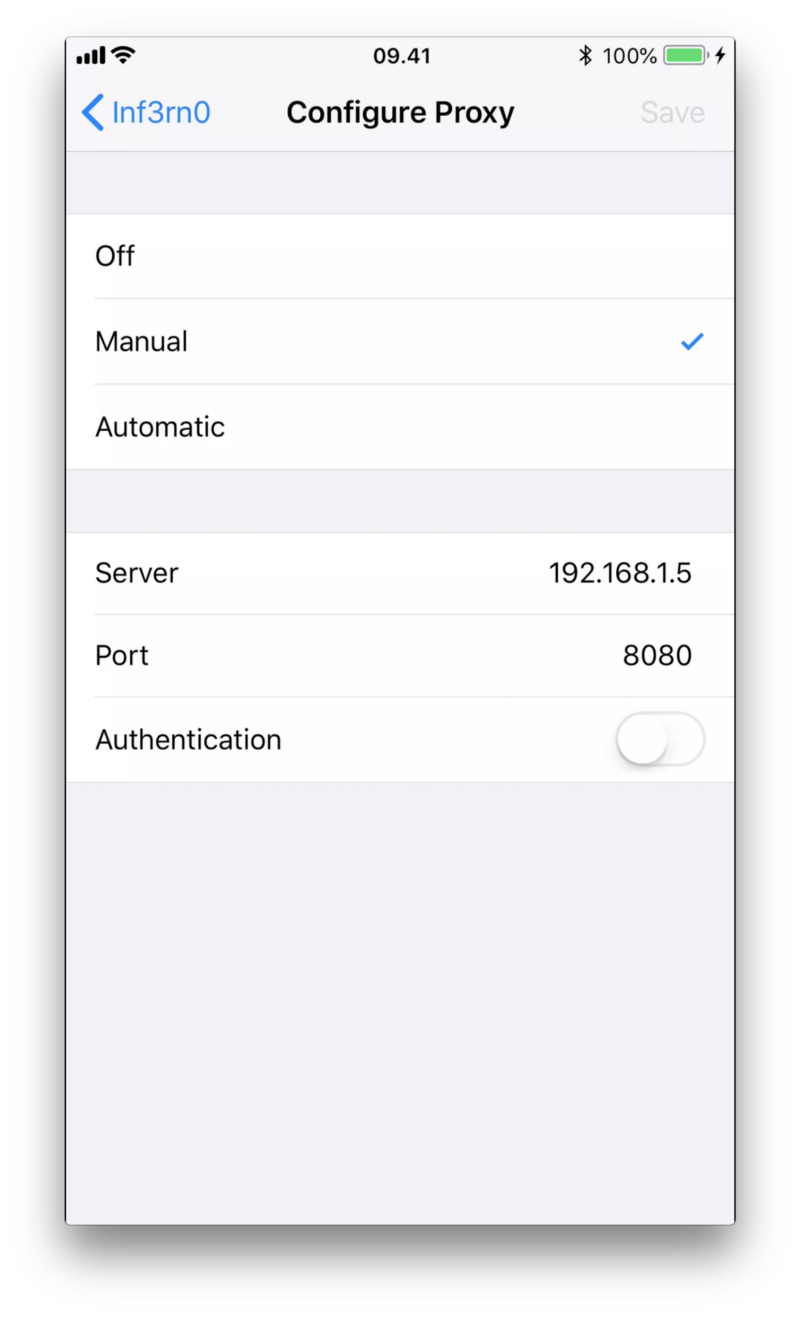
- Open
Settings > Wifi > <your_wifi_name> > Tap on Configure proxy under HTTP proxy - Select
manualand enter the mac machines IP address in Server and default port as8080. For now leaveAuthenticationturned off
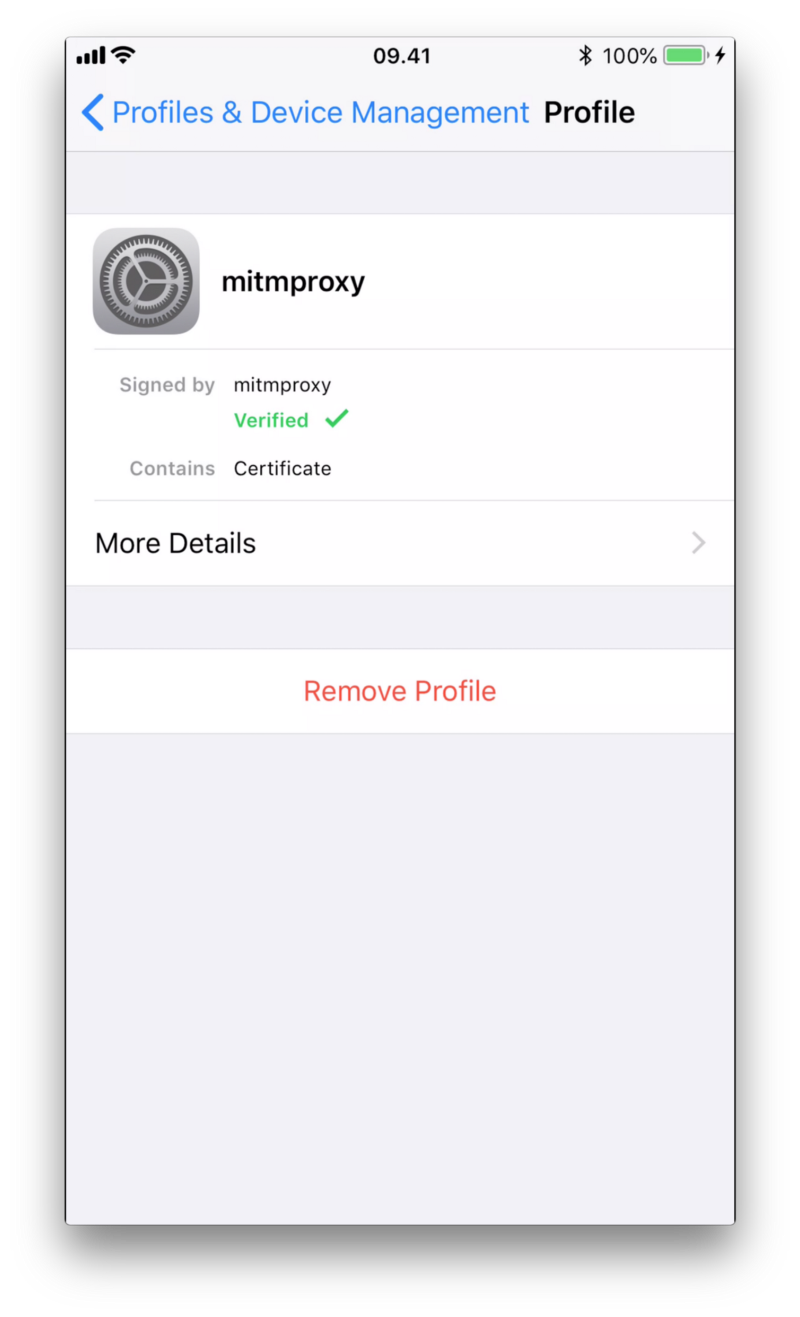
- Open
mitm.iton any browser in real device and tap onApple iconfollowed by tappinginstallcouple of times to installmitmproxy certificateon the device - After setup verify certificate profile is setup by navigating to
Settings > Profile and Device Managementand verifyingMITM proxyis listed in list of certificates
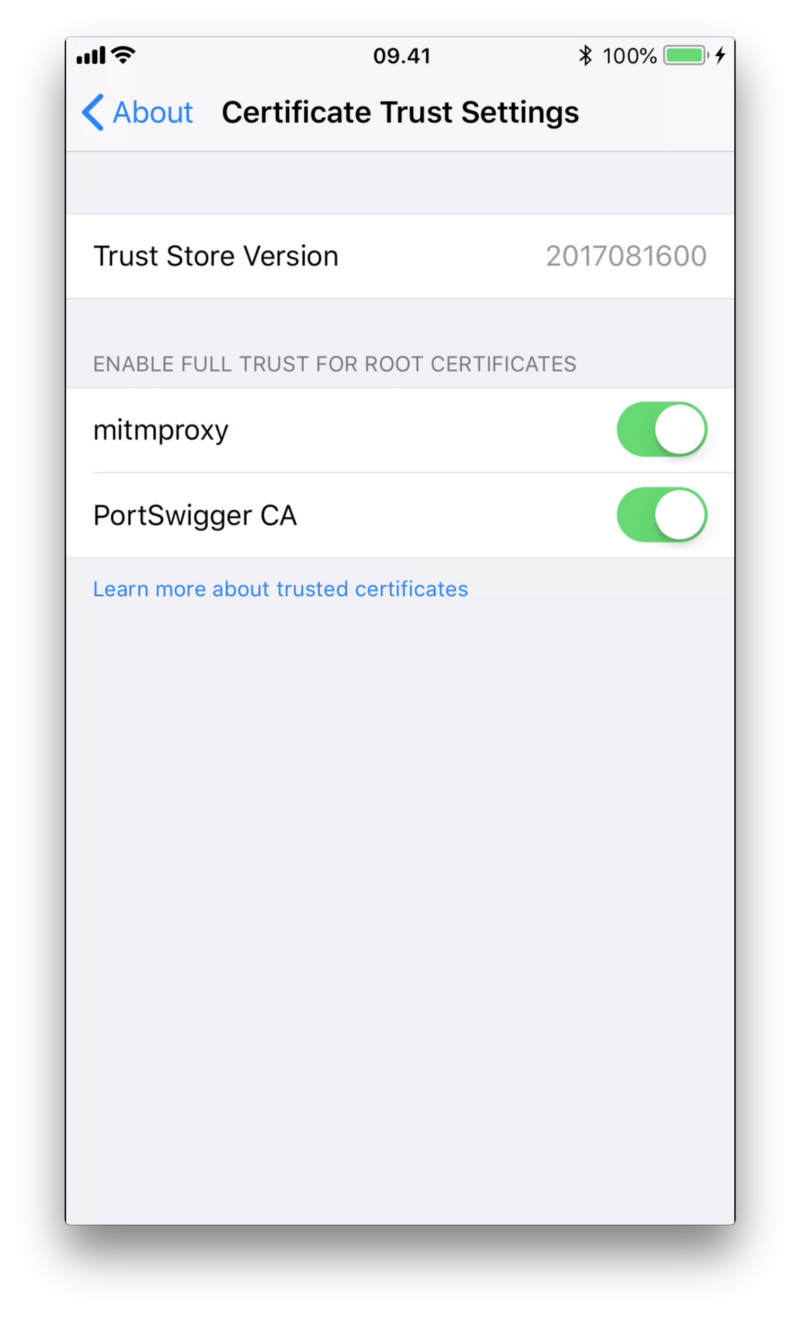
- Finally ensure for MITM proxy, Full trust is enabled for root certificate the installed
certificate by navigating to
About > Certificate Trust Settings
How to see logs
- Once MITM is running in terminal you would start seeing network calls having all requests, response and header info captured.
- Navigate to the call that you want to see the response for and then press enter
Tip: If you want to see calls made by your apps with a specific pattern in the URL type
<strong><em>f</em></strong>and then enter a pattern, this would filter out all other captured network calls.
- To see all available commands, press
?to see a summary of available commands.
That’s it. Enjoy! Do revert in case you have any specific questions on this and lets figure them out together
Comments